Infosec Industry News
A collection of Infosec latest news, analysis and best practices from top business influencers and the world's most trustworthy sources.

CFTC proposes rules to evaluate prediction market risks
Key takeaway: The Commodity Futures Trading Commission has proposed a rule that would establish a framework to help the agency determine whether prediction market contracts are contrary to the public interest and thus invalid. Expert quote: 'This…
Why soaring memory prices could be Nvidia's next big advantage
Rising memory prices are making AI infrastructure more expensive — and Nvidia's biggest customers could be in for serious sticker shock. Last month, Meta CEO Mark Zuckerberg and Microsoft CFO Amy Hood cited rising memory costs for chips and…

Oracle Addresses PeopleSoft Vulnerability Amid Reports of Zero-Day Attacks
Oracle on Thursday released an out-of-band advisory addressing a PeopleSoft vulnerability that can be exploited by an unauthenticated attacker for remote code execution. The security alert comes amid reports that the notorious ShinyHunters hacker…

OnyxC2 Stealer Offers Cybercriminals Enterprise-Grade Theft for $250 a Month
The OnyxC2 stealer surfaced on a cybercrime network earlier this year and is available through Malware-as-a-Service (MaaS) for hire starting at $250 per month. The rental price for OnyxC2 is at the higher end of stealer costs. This is primarily…

Is PPG Industries Stock Underperforming the Nasdaq?
PPG Industries, Inc. (PPG), headquartered in Pittsburgh, Pennsylvania, manufactures and distributes paints, coatings, and specialty materials. Valued at $25.2 billion by market cap, the company makes protective and decorative coatings, flat glass…

CISA Directs Federal Agencies to Prioritize Security Patches Based on Risk
The US Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday announced a new directive that requires federal agencies to prioritize patching the highest-risk security flaws. CISA established the Known Exploited Vulnerabilities (KEV)…

Siemens Says Desigo CC Files Flagged as Malware by Security Engines
Siemens is informing customers that patch files for its Desigo CC building management system are erroneously being flagged as malware by multiple cybersecurity solutions. Desigo CC integrates HVAC, lighting, security, fire safety, power, and other…
Novartis delpacibart braxlosiran (del-brax) Phase I/II study in facioscapulohumeral muscular dystrophy (FSHD) meets primary biomarker endpoint
Ad hoc announcement pursuant to Art. 53 LR FORTITUDE study met primary and key secondary endpoints of reduction in KHDC1L and creatine kinase levels, with safety profile consistent with previous results Del-brax indicates potential to become the…

Hackers Exploit Langflow Vulnerability for Remote Code Execution
Threat actors have begun exploiting a high-severity vulnerability in the popular low-code AI development platform Langflow, according to VulnCheck. Tracked as CVE-2026-5027 (CVSS score of 8.8), the security defect is described as a path traversal…
Uber now keeps most of the fare from your ride in some cities, according to a new driver study
More of your Uber fare is going to the company than the driver, according to a new study. Uber's 'take rate,' or the percentage of each fare that the company hangs on to, has risen above 50% this year in some cities, according to an analysis by Len…

Israeli startup Aryon Security raises $25m
Israeli startup Aryon Security, which last year unveiled its innovative cloud security solution, has completed a $25 million Series A financing round, which brings the total amount raised by the company since it was founded in late 2024 to $38…

FBI Seizes 13 Websites That Officials Say Were Used by China to Target and Recruit US Workers
The FBI has seized more than a dozen websites that officials say were part of a Chinese effort to target American workers who have access to classified or sensitive government information, the Justice Department said Wednesday. The 13 websites…
Man Group PLC : Form 8.3 - JTC Plc
PUBLIC OPENING POSITION DISCLOSURE/DEALING DISCLOSURE BY A PERSON WITH INTERESTS IN RELEVANT SECURITIES REPRESENTING 1% OR MORE Rule 8.3 of the Takeover Code (the “Code”) (a) Full name of discloser:Man Group PLC(b) Owner or controller…
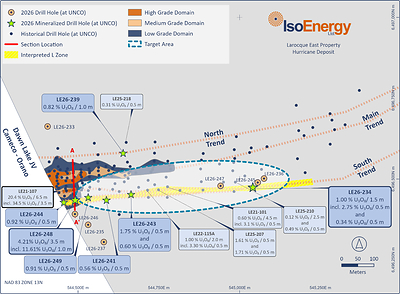
IsoEnergy Commences 8,000 Metre Summer Drill Program at the Larocque East Project, Athabasca Basin
TORONTO, June 11, 2026 /CNW/ - IsoEnergy Ltd. ('IsoEnergy', or the 'Company') (NYSE American: ISOU) (TSX: ISO) is pleased to announce the commencement of its 2026 summer exploration program on the Larocque East project (the 'Project'), which hosts…

Truoux Establishes Data Security Standards and Privacy Protection Mechanisms | Metaverse Post
Trust crises caused by data breaches continue to spread in the financial sector, and investors are increasingly aware of the importance of information security. Recently, Truoux Exchange has upgraded its data encryption system, hierarchical…
Receive a Daily briefing on Infosec Industry News
Get Started